Why Cross‑Site Scripting XSS Matters for Businesses and Users
In today’s digital economy, web applications power everything from online banking to social platforms. Alongside their utility, they attract increasingly sophisticated cyber threats, and among the most persistent is Cross‑Site Scripting (XSS). This dangerous vulnerability is responsible for countless data breaches, session hijacks, and compromised accounts worldwide.
Understanding how XSS works, why it matters, and how to stop it is essential for safeguarding digital assets. In this guide, a cybersecurity consultant breaks down the core concepts, risks, and proven strategies to defend your web applications. Whether you’re a business owner, developer, or enterprise leader, you’ll walk away with actionable insight to protect your systems in 2026 and beyond.
What Is Cross‑Site Scripting (XSS)?
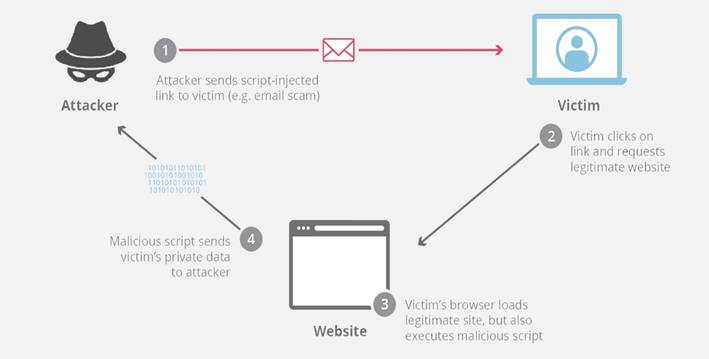
Cross-site scripting (XSS) is a type of injection attack where the attacker attaches code to a legitimate website that will execute when the victim loads the website. That malicious code can be inserted in several ways. Most popularly, it is either added to the end of a URL or posted directly onto a page that displays user-generated content. In more technical terms, cross-site scripting is a client-side code injection attack.
The reason XSS remains dangerous is simple: most browsers inherently trust the code that originates from a website they are displaying. If that website fails to validate or encode user‑generated inputs, an attacker can embed harmful JavaScript that executes automatically in another user’s browser.
This problem is not theoretical. Research shows that more than 60% of web applications are statistically vulnerable to XSS flaws due to inadequate input sanitization and poor secure coding practices. That prevalence underscores why a data security consultant is crucial for risk identification and mitigation across complex digital environments.
Related: Wiz Cloud Security In 2026: Trends, Innovations, And Enterprise Adoption
How Cross‑Site Scripting Works
To understand XSS, think of a typical form or search field on a website. When users enter text into an input field:
- The browser sends that input to the server.
- If the web application includes that input in its HTML output without proper filtering, it effectively returns malicious code back to other users.
- The victim’s browser then executes this code, unknowingly trusting it as legitimate content.
Attackers exploit this behavior by disguising harmful JavaScript as benign input, ultimately co‑opting user sessions or stealing sensitive credentials. A data security consultant would point out that these vulnerabilities often originate from weak input validation, missing output encoding, or outdated libraries that don’t enforce strict security standards.
Types of Cross‑Site Scripting Attacks
XSS is not a single, uniform vulnerability; it comes in multiple flavors, each with distinct characteristics and threat vectors.
Stored XSS (Persistent XSS)
Stored XSS occurs when a malicious script is saved directly on the target server, for example, in a database, message board, or comment section. When other users access the affected page, the script executes in their browser. Stored XSS is particularly dangerous because the payload persists, potentially compromising many users once triggered.
Reflected XSS (Non‑Persistent XSS)
Reflected XSS happens when user input is reflected back immediately within the web application’s response. An attacker typically sends a malicious URL that includes a harmful script. When an unsuspecting user clicks that link, the script returns immediately in the site’s response and executes in the browser.
DOM‑Based XSS
In DOM‑based XSS, the vulnerability exists in the client‑side code. The browser’s Document Object Model (DOM) manipulates data from untrusted sources without proper encoding, allowing scripts to run outside of server‑side validation mechanisms. This form is often harder to detect with traditional scanning tools, but it still poses a significant risk.
Related: 5 Cybersecurity Trends To Watch In 2026
Why XSS Attacks Are So Prevalent
Despite advances in secure development tools, XSS remains one of the top web vulnerabilities.
According to security research, XSS vulnerabilities are found in nearly two‑thirds of all web applications, largely due to insufficient input validation and complex dynamic interfaces that rely heavily on JavaScript.
The OWASP Top Ten, a widely respected ranking of web security risks, consistently includes XSS among the most common and exploitable issues, owing to its continued presence in applications of every scale and sector.
That enduring prevalence is precisely why organizations invest in cybersecurity consultant professionals trained to conduct security assessments, risk analyses, and vulnerability remediation tailored to real‑world threats.
Related: What Is Vishing? A Cybersecurity Consultant’s Guide To Phone-Based Social Engineering
Risks and Impact of XSS Attacks
The consequences of a successful XSS exploit can range from mild annoyance to catastrophic breach.
- Session Hijacking: Attackers can capture session tokens and impersonate legitimate users.
- Credential Theft: Login details and authentication cookies can be exfiltrated.
- Malware Delivery: Malicious scripts can redirect users to exploit kits or malware downloads.
- Data Theft: Sensitive information visible in the user’s browser may be stolen.
- Reputation Damage: A compromised application loses customer trust and business credibility.
Because most XSS attacks manipulate the browser’s trusted context, traditional security controls like firewalls may be insufficient without a layered defense strategy informed by expert consultants.
Related: What Is Public Key Infrastructure? A Complete Guide For Cybersecurity Professionals
Real‑World Examples
Consider a social networking site that allows users to post comments without rigorous filtering. An attacker could submit a comment containing a script that steals cookies from visitors. When others load the page, their browsers execute the script, and the attacker gains access to active sessions, potentially compromising email, financial accounts, or business dashboards.
Or imagine an online banking platform that reflects user input in error messages without encoding. If an attacker crafts a URL with embedded JavaScript and persuades a user to click it, that script could redirect to a phishing page or capture two‑factor authentication tokens.
These scenarios are not hypothetical; they mirror known XSS exploits that continue to plague unprotected sites and services.
How a Cybersecurity Consultant Identifies XSS Vulnerabilities
Preventing Cross-Site Scripting (XSS) requires a strategic and comprehensive approach that goes beyond basic testing. A cybersecurity consultant identifies XSS vulnerabilities through multiple methods. They begin by conducting thorough security audits of web applications to uncover hidden weaknesses.
Next, they perform penetration testing using a combination of automated tools and manual exploratory techniques to simulate real-world attacks. Reviewing the application’s source code is also essential, as it helps detect unsafe patterns like unescaped input or insecure library usage.
Additionally, consultants evaluate frameworks and third-party dependencies to ensure no outdated components prone to XSS are in use. Finally, they leverage specialized vulnerability scanners designed to detect DOM-based, reflected, and stored XSS vectors. By combining these strategies, organizations can proactively close security gaps before attackers have the chance to exploit them.
Related: What Is OT Cybersecurity And How It Prevents Industrial Cyber Attacks?
Prevention Techniques for Cross‑Site Scripting
To mitigate XSS risks effectively, developers and security teams should adopt the following best practices:
Input Validation and Sanitization
Ensure that all user inputs are strictly validated and sanitized before processing. Reject unexpected content or encode it safely if necessary.
Output Encoding
Before rendering user‑supplied data in HTML, CSS, or JavaScript contexts, encode it properly to prevent execution.
Content Security Policy (CSP)
Implement strict CSP headers to limit the domains that scripts can execute from, reducing the impact of injected scripts.
Secure Coding Practices
Follow frameworks and guidelines such as OWASP’s XSS Prevention Cheat Sheet, which outlines secure patterns for common languages and environments.
Regular Security Scanning
Use dynamic and static tools to continuously monitor for vulnerabilities and regressions introduced during updates.
Related: What Is (MITM) Man In The Middle Attack In Cybersecurity?
Why Your Business Needs a Data Security Consultant
Cross‑Site Scripting is just one of many threats facing modern applications. As attack vectors grow more complex and frequent, having dedicated expertise is no longer optional.
A data security consultant helps you:
- Prioritize security investments based on real risk.
- Build resilient and compliant systems.
- Respond swiftly to incidents and breaches.
- Educate teams on cyber risk awareness and best practices.
Their role goes beyond checking boxes; they help future‑proof your digital assets against threats like XSS and emerging browser‑based attacks.
Strategic Defense Against XSS Attacks
Cross‑Site Scripting remains one of the most common and dangerous vulnerabilities in web applications today. Its ability to run malicious code in the context of trusted sites makes it a favorite tool for attackers seeking to steal data, hijack sessions, or damage business reputation.
Protecting against XSS demands informed strategy, disciplined secure coding, and ongoing vigilance, ideally supported by experienced cybersecurity consultants USA Like Dr. Ondrej Krehel, who know how attackers think and operate.
By implementing robust validation, encoding, and layered defenses, you can dramatically reduce your exposure to XSS and fortify your web applications against the next generation of cyber threats.
Related: What Is a Multimodal Large Language Model?
FAQs Section:
1. What is XSS?
XSS is a type of attack where malicious scripts run in a user’s browser via trusted websites, stealing data or hijacking sessions.
2. What are the types of XSS?
- Stored: Script saved on the server.
- Reflected: Script sent in a URL and executed immediately.
- DOM-based: Script runs through client-side code.
3. Why is XSS common?
Weak input validation, complex JavaScript, and outdated libraries make web apps vulnerable.
4. How can XSS be prevented?
Use input validation, output encoding, Content Security Policies, secure coding, and regular security scanning.
5. Why hire cybersecurity consultants?
They detect hidden vulnerabilities, guide secure coding, and implement defenses to protect against XSS attacks.

